Routing data at the tactical edge
StoryMarch 07, 2012
High-bandwidth tactical communications look to IP for connectivity, but data security concerns with such protocols loom large.
As military networks reach out to individual soldiers and their vehicles at the tactical edge, the promise for intelligence and command and control is great, but so are the risks unless security is built in from the ground up.
Despite the specter of budget cuts and program cancellations, the U.S. military continues to stress high-speed, high-bandwidth, agile, and secure communications. The first strategy-based equipment imperative listed in the Army Modernization Plan 2012 is “network the force.” Of the handful of mission-critical systems identified in that document, four focus on communications or information superiority.
U.S. forces envision bandwidth-hungry transactions such as HD video feeds in the tactical space. Programs and concepts have emerged to support such aims, including the proliferation of high-speed communications and processing nodes on the battlefield. This expansion of tactical connectivity, however, is based on IP, a core component in commercial-enterprise architectures but a magnet for attacks.
IP vision
The first “critical” program listed in the Army Modernization Plan 2012 is the Joint Tactical Radio System. This family of Software-Defined Radios will provide tactical end-to-end IP data and voice communications. These include the Warfighter Information Network-Tactical, an IP-based broadband backbone; the Ground Combat Vehicle, which will exploit networking advances; the Army’s portion of the Distributed Common Ground/Surface System for intelligence information access; and the Joint Battle Command-Platforms effort that involves integration of computer hardware and software and networking capability into tactical vehicles, aircraft, and dismounted forces.
High-bandwidth tactical communications would be a force multiplier, improving coordination in the field. Multiple tanks or armored vehicles, for example, each equipped with a router to connect the nodes, could set up a mesh network for data sharing. Some of the vehicles might also be equipped with powerful cellular and satellite links to communicate with dismounted soldiers or over longer distances. The vehicles could also serve as processing nodes for dismounted soldier applications.
The tactical “cloud” computing environment described in the preceding example could support applications such as facial recognition. Soldiers could transmit photos of persons via smartphones to determine whether those persons should be detained. Tactical cloud resources could be distributed between forward bases and mobile assets. Current concepts envision routers and processors embedded in ground vehicles, drones, airplanes, ships, and satellites.
Challenges
Deployment won’t be easy. The common attacks that bedevil the commercial IP world – where bandwidth is high and reliable, links are fixed, and processing and storage resources are generous and stationary – are more likely and dangerous in a hostile environment where bandwidth is uncertain, assets mobile, and resources limited. Moreover, IP was built for openness. Hackers cut their teeth on Internet Denial of Service (DoS), spoofing, and malware attacks.
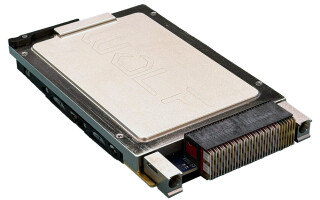
Many security measures are already in place, using physical and procedural protection, encryption, authentication, and other techniques. However, new attacks are invented every day. Government-sponsored or subsidized attacks would also be likely in a hostile environment. That is why routers – the heart of the network – are adding firewall and intrusion detection hardware and software, building in security at the ground floor. An example of these emerging products is the GE Intelligent Platforms RTR8GE, a small, rugged, intelligent IP router with tunable security, using the COTS-hardened Junos OS (Figure 1).
Figure 1: RTR8GE rugged, intelligent IP router from GE Intelligent Platforms
(Click graphic to zoom by 1.9x)
Technology dividends
Routers are more intelligent than switches. They can detect errors, retransmit packets, and change data paths, depending on the circumstances. But modern secure routers can do much more. Using hardware-based Deep Packet Inspection (DPI), these devices can scan packets from the physical to the application layer, for example, flagging a word in an email message. Whereas software-based DPI struggles to keep up with the line rate, hardware-based DPI can monitor data flows without inducing crippling delays.
Emerging technologies, such as Radio Aware Routing (RAR) protocols, allow the router to monitor link status and reliability. The router will be able to choose the best link – satellite, cellular, or traditional ground radio – and the best path to the destination. As the quantity and variety of wired nodes grow, network bandwidth and reliability are enhanced. The RAR and similar protocols will help enable the goal of secure mobile ad hoc networking, allowing fast, networked communications.
For more information, contact Charlotte at [email protected].