Integrating a secure, tactical, Type 1 hypervisor on an OpenVPX SBC
StoryMay 07, 2021

By Steve Edwards and Mike Mehlberg
An industry perspective from Curtiss-Wright Defense Solutions
The number of boards and servers deployed on a military system can be reduced drastically by using a Type 1 hypervisor.
Virtualization improves cyber resiliency: A quick clone and replacement of one or more virtual machines can near-instantly get a damaged system back up and running with minimal loss of mission capability. Embedded operating systems can be chosen (and secured) for their particular mission requirements. Instead of installing a full-function enterprise version of Linux, a specific distribution can be selected for the mission at hand and secured accordingly.
An example of a secure virtualization solution for advanced mission computing and radar systems is Wind River’s Titanium Secure Hypervisor, which is specifically designed for hostile computing environments. The hypervisor leverages hardware-based root-of-trust to perform a secure boot process and can optionally leverage hardware-provided security services at runtime. During system operation, the hypervisor enforces physical and logical isolation. Software loads execute within private enclaves, even though they may be running on a single physical processing board. With strong technology and anti-reverse-engineering protections built in a hypervisor can ensure that sensitive applications and data remain protected against unauthorized access, theft, and malicious modification.
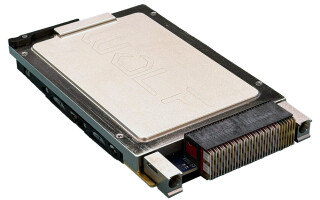
A hypervisor can be easily preintegrated onto an OpenVPX single-board computer (SBC); the integration process can be done in less than a day and designed securely for specific missions:
- Verify the peripheral configuration: Ensure the onboard and their associated drivers support virtualization, utilize well-established DMA channels and (memory) ranges, and are free of lurking issues such as transparent PCI-E switches, which require special handling in a virtualized environment.
- Configure the BIOS/UEFI:
- Within the BIOS/UEFI, the onboard peripherals need to be configured for passthrough.
- The OS or hypervisor loaded on the SBC will need to access the peripherals (either thru direct passthrough, Intel’s VT-d instructions, or as a purely virtual device) and cannot do so unless this configuration is set.
- Next, set up legacy emulation for the environment so older operating systems can utilize legacy hardware exposed through newer interfaces.
- Finally, disable hyperthreading for performance and security reasons. Despite the performance improvements hyperthreading provides, various side-channel attacks exist in virtualized environments. Also, tying specific processors (physical cores) to specific virtual machines enables predictable performance and security.
- Enable Intel virtualization bits: The CPU’s built-in hardware virtualization acceleration might need to be explicitly turned on within the system BIOS/UEFI. Confirm these for high-performing, secure virtualization: Intel VT-x, which enables the virtual machines to leverage hardware-acceleration features built into the Intel chipset; Intel VT-d, which enables the virtual machines to directly access peripheral devices and restrict guest access to specific peripherals, plus enables PCI device passthrough and IOMMU configuration; and Intel-TXT, Intel’s trusted boot mechanism that’s used with virtualization to ensure proper authenticated machine boot.
- After enabling these features in BIOS, they must be verified as operational in a guest or hypervisor. This testing and integration ensures that the hypervisor can access all of the hardware and identify any present/enabled features.
• Install the hypervisor to local storage: The virtualization software must be installed onto the SBC so control is transferred to it during the boot process. In the case of a Type-1 hypervisor it’s necessary to install a base OS to act as the control domain, such as Linux. The hypervisor is then installed in conjunction with the OS, where the actual hypervisor is added to the boot environment, and the actual control domain is established. Any drivers and/or BSPs must be installed for any peripherals used by the hypervisor, either directly or indirectly.
• Install Linux: Before boot and verification, the guest operating system must be installed. In this example, Linux is used for the guest VM(s). After the board support package is configured (in the guest this time), a secure configuration is forced using virtualization extensions and the associated provisioning tools.
This entire process of integrating virtualization onto an SBC can be accomplished in as little as four hours. In this example, there were zero modifications to the software and minimal tweaks to the hypervisor, mostly related to the heuristics used for various virtualization detections.

Steve Edwards is Director of Secure Embedded Solutions for Curtiss-Wright.

Mike Mehlberg leads sales and marketing for Star Lab, Wind River’s Cybersecurity and Technology Protection Group.
Curtiss-Wright Defense Solutions
https://www.curtisswrightds.com/
Star Lab, a Wind River company
https://www.starlab.io/