GUEST BLOG: Drone warfare and Launched Effects - Blog
January 29, 2026WARFARE EVOLUTIONS BLOG. Now is a good time to add some new words to your vocabulary: Launched Effects (LE). The war in Ukraine started in February 2022 and has developed into a new form of warfare with drones. Ukraine has launched as many as 9,000 drones at Russian positions in one day, and Russia has launched as many as 6,400 drones in one day at Ukrainian positions. About 75% of the casualties and equipment destroyed in Ukraine have been attributed to drones. Ukrainian drones have flown as far as 1,500 miles to hit targets inside Russia. Russian drones have traveled as far as 1,000 miles to hit targets inside Ukraine.
GUEST BLOG: Looking at the European and Pacific military markets - Blog
October 30, 2025WARFARE EVOLUTION BLOG. Before we jump to another topic in these articles, it would be appropriate, relevant, and instructive if we conclude this series on the worldwide military markets by looking at NATO in Europe, and the spending by military alliances and security agreements in the Pacific area. The SIPRI report (Stockholm International Peace Research Institute) does a nice job of breaking down the regional military markets if you need more details than we cover here. Put this information under demand-side data in your collection.
GUEST BLOG: The supply-side of the worldwide military markets - Blog
August 01, 2025WARFARE EVOLUTION BLOG: Last time, we built the worldwide military market demand-side tree diagram. By now, you should have drawn that diagram and filled-in the roots and branches with the data revealed in the previous articles. This time, we will build the supply-side tree diagram and integrate the two. When we complete this task, don’t try to add-up the supply-side and demand-side numbers and expect them to balance or even come close. The market research reports mentioned count things differently, and they estimate lots of numbers. These people are not certified public accountants.
GUEST BLOG: The demand-side of worldwide military markets - Blog
April 24, 2025WARFARE EVOLUTION BLOG: The time has arrived for us to pull together the previous eight articles about the worldwide military platform markets, and organize that data in a clear and informative manner. We could spreadsheet all these numbers and produce some scatter plots or bubble charts. But, they seem so cold and dull. So, let’s take a more aesthetic and artistic approach, the "feng shei statistical analysis method” using balance and harmony. That requires a modified tree diagram. Everybody loves a good tree diagram.
GUEST BLOG: Questions about: SR-72 aircraft, 6G NGAD fighter plane, and B-21 Stealth Bomber - Blog
November 26, 2024WARFARE EVOLUTION BLOG: Let’s take a break from exploring the worldwide markets for military platforms in these essays, and connect some dots between the SR-72, the (Next Generation Air Dominance) fighter plane, and the B-21 Bomber. From the latest news reports, they all seem to be related. Dissecting each of these platforms should give us a better understanding of what’s going on inside the U.S. Air Force.
The worldwide market for military satellites and helicopters - Blog
September 26, 2024WARFARE EVOLUTION BLOG. In my previous seven articles, we explored the worldwide markets for most military platforms. However, there are two platforms left to complete our study – satellites and helicopters. I saved these two segments for last since they share some common characteristics. Satellites expend their limited fuel struggling to stay in orbit (station keeping) while helicopters use their fuel thrashing the air furiously with rotor blades to stay aloft. Both fight a constant battle against gravity so that’s why I put them together for this essay. As they say in the aviation community: airplanes want to fly, but satellites and helicopters don’t.
GUEST BLOG: The worldwide markets for military radar, sonar, electronic warfare, and communications - Blog
July 30, 2024WARFARE EVOLUTION BLOG: So far in this series, we have explored the worldwide markets for military platforms (tanks, ships, submarines, airplanes, and drones). These segments are interesting to the companies that bend metal, but for us, we want to know about the electronic systems inside those platforms. That insatiable yearning is the inspiration for this article. There’s a plethora of these systems, scattered around the services, so we can’t identify all of them here. I'll just mention the major programs and let you discover the rest on your own.
GUEST BLOG: The worldwide market for unmanned aerial vehicles - Blog
April 30, 2024WARFARE EVOLUTION BLOG. Previously, we studied the markets for fighter planes and bombers, ground combat vehicles and tanks, warships and submarines, and unmanned naval vessels (surface and underwater). Now, it’s time to explore the market for unmanned aerial vehicles (UAVs), which is rapidly becoming the largest volume segment of the military platforms. First, the UAV designation is actually a misnomer.
The worldwide market for unmanned naval vessels - Blog
February 29, 2024WARFARE EVOLUTION BLOG. In our last escapade, we investigated the worldwide market for warships and submarines. Out of respect for the literary principle of subject matter continuity, we are forced to explore the worldwide market for UNVs (unmanned naval vessels) in this essay, since they are an extension of warships and submarines. UNVs break down into two basic groups: unmanned surface vessels (USV) and unmanned underwater vehicles (UUV). We will deal with naval unmanned aerial vehicles (NUAV) in another composition.
GUEST BLOG: Worldwide Market for Warships and Submarines - Blog
November 29, 2023WARFARE EVOLUTION BLOG. In previous episodes, we explored the two largest military platform markets: ground combat vehicles and tanks, and fighter planes and bombers. This time, we’ll take a look at the third market for big iron: warships and submarines. I’m going to throw a lot of numbers around in this composition but don’t take them as absolute. Warships sink all the time (Ukraine has sunk or damaged 17 Russian ships in the war so far), and shipyards are launching a new warship now and then. So, look at these numbers as estimates. Let’s start from the top.
The global market for fighter planes and bombers - Blog
August 30, 2023WARFARE EVOLUTION BLOG. Last time, we looked at the market for ground combat vehicles and tanks. Now, it’s time to look at the second largest volume platform market in the military: fighter planes and bombers. Let’s start at the top. According to Flight Global, there were about 53,250 military aircraft in the world in 2021. The U.S. flies about 25% of that total (13,250), Russia flies 8% (4,170), and China flies 6% (3,280). This includes fighters, bombers, tankers, cargo planes, ISR (intelligence, surveillance, and reconnaissance) planes, and helicopters. Keep in mind that these numbers move around. Military aircraft crash all the time, and Russia has lost about 175 aircraft in Ukraine in 16 months.
The worldwide market for military ground combat vehicles and tanks - Blog
June 29, 2023WARFARE EVOLUTION BLOG. In our last adventure, we explored the worldwide military markets using three recent reports, and integrated those into the TAM-SAM-SOM model (total addressable market, serviceable addressable market, and serviceable obtainable market). That expedition gave us a macro-view of things. Now, it’s time to put on our rubber gloves, get out the sharp knives, and carve the military market into edible segments. The most objective way to dismember this massive creature is to cut it up by platform, so we’ll start with the largest volume segment: ground combat vehicles (GCV) and tanks.
The $600 billion market for military weapons, sensor systems, and platforms - Blog
April 27, 2023WARFARE EVOLUTION BLOG. As previously promised, we are fearlessly embarking upon a challenging project here, to integrate the demand-side and supply-side data about the world military markets. The best method to attack this problem is from the top-down. Going from the bottom-up would create debilitating confusion, misconceptions, and illusions.
Army Project Convergence 2023 exercises canceled, and UFOs take a high-speed turn - Blog
March 14, 2023WARFARE EVOLUTION BLOG. As I was putting together my notes about all the Army’s Project Convergence Exercises, I got a notice that the planned PC-23 exercises had been cancelled and rescheduled for 2024. That’s a great disappointment, so let's drown our sorrows in a vintage bottle of data from the three previous exercises: PC-20, PC-21, and PC-22.
Cryptanalysis, "Ulysses," dolphins, and talking to extraterrestrials - Blog
November 30, 2022WARFARE EVOLUTION BLOG. Let’s take a break from studying the Kill Web and explore something else. Back in the late 1940s, Harvard linguist George Kingsley Zipf picked up a copy of James Joyce’s novel “Ulysses” and read it. Although it was acclaimed by the pompous literary pundits in rumpled suits as a masterpiece, Zipf could not believe how incomprehensible and boring it was. In case you were not exposed to it in college, reading “Ulysses" is like being mercilessly waterboarded with the English language by shallow characters, in a dull story with no detectable plot, for an unbearable period of time.
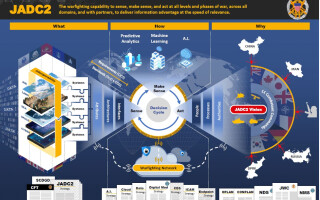
JADC2 and the Kill Web - Blog
September 30, 2022WARFARE EVOLUTION BLOG. If you have been a fervent reader of these Kill Web articles, you know that the Army has been connecting their sensors and weapons together into a tactical network under their IBCS initiative (Integrated Battle Command System). The Navy has been secretly connecting their ships and planes together with their CEC program (Cooperative Engagement Capability). The same goes for the Air Force’s planes under their ABMS initiative (Advanced Battle Management System) and the Space Force’s satellites (SF-ABMS).
The Air Force, ABMS, and the Kill Web - Blog
July 28, 2022WARFARE EVOLUTION BLOG. So far, we have covered the Army (IBCS), the Navy (CEC), and the Space Force (SF-ABMS) programs. So now it’s time to explore what the Air Force is doing to join the Kill Web. Their primary effort is called ABMS (Advanced Battle Management System), that seeks to connect all their aircraft, weapons, and sensors together into a tactical mesh network where they can talk to each other in real time. Maybe the best way to present this information is by comparison to what the other services have been doing. That might be more informative.
The Space Force, Lagrange points, xenomorphs, and the Kill Web - Blog
April 28, 2022WARFARE EVOLUTION BLOG. So far, we have studied how the U.S. Army (IBCS) and Navy (CEC) programs have been conducting experiments, to integrate their weapons and ISR (intelligence, surveillance, and reconnaissance) systems into the Kill Web mesh network. Now, let’s take a look at what the Space Force is doing. The Space Force was formed as the fourth armed service in 2019 and operates under the Air Force.
The Navy, CEC, Project Overmatch, and the Kill Web - Blog
February 26, 2022WARFARE EVOLUTION BLOG. Last time, we looked at the Army’s IBCS (Integrated Battle Command System) program and Project Convergence exercises, through the eyes of their advanced AI (artificial intelligence) Kill Web algorithms (Rainmaker, Prometheus, FIRESTORM, and SHOT). Unfortunately, the Navy doesn’t talk much about AI algorithms, so that forces us to reluctantly abandon the trusted engineering principle of consistent analytical continuity and view their progress through what they do talk about: their platforms.
How Rainmaker, Prometheus, FIRESTORM, and SHOT AI algorithms enable the Kill Web - Blog
December 23, 2021WARFARE EVOLUTION BLOG. In our previous adventure, I introduced the pyramid model to identify each service’s Kill Web program and their experimental activities. Sitting at the peak is the Pentagon’s JADC2 program (Joint All Domain Command and Control) and the GIDE-XX exercises. On one side is the Army's IBCS program (Integrated Battle Management System) and Project Convergence exercises. On the next side is the Navy’s CEC program (Cooperative Engagement Capability) and their highly classified Project Overmatch exercises. On the next side is the Air Force's ABMS program (Advanced Battle Management System) and Onramp exercises. Since the Space Force stills falls under the Air Force, we’ll call their program SF-ABMS. They make up the final side of the pyramid. Space Force has been conducting a number of experiments under different names so we’ll decode those in the future.