Red Hat
Raleigh, NC 27601 https://www.redhat.com/en/solutions?sc_cid=701f2000001D7iwAAC&gclid=CjwKCAiAy9jyBRA6EiwAeclQhMNNOYXJJI7EX95tSfkQcPGM0QJr6afI0qwH6Jn78zREM6oUPFXDHBoCOb4QAvD_BwE&gclsrc=aw.ds

GUEST BLOG: Bringing data processing to the extraterrestrial edge - Blog
February 13, 2024When it comes to data processing and analysis, space is a final frontier that’s filled with challenges. Fortunately, military leaders have access to the technology and tools to make interstellar data processing a success, resulting in faster actionable insights – and a strategic and tactical advantage.
How automation can optimize zero-trust security at the multidomain, tactical edge - Story
August 04, 2023The U.S. Department of Defense (DoD)is investing in multiple initiatives including the Joint Warfighting Concept (JWC) and Combined Joint All-Domain Command and Control (CJADC2) to enable coordinated military operations against current and future threats. Because these efforts involve the integration of devices and data streams at the tactical edge, they call for a zero-trust approach to cybersecurity. But achieving zero trust at the edge presents multiple challenges. One path to overcoming these barriers is an automation strategy that enables more rapid and reliable configuration of components and helps achieve data-sharing across echelons with greater security.
GUEST BLOG: How the military can speed data mobility for smart decisions on the move - Blog
February 03, 2023The military is producing ever-larger amounts of valuable data from embedded systems at the edge. Now it needs more effective ways to share, understand, and act on that data – at or near the user and as close as possible to real time. By leveraging available technologies like containerization and tools to manage them, warfighters have the opportunity to make faster, smarter decisions where and when they’re needed to help achieve battlespace dominance.
Three keys to frictionless zero-trust security - Blog
August 23, 2021By Mike Epley, Red Hat
The U.S. Department of Defense (DoD) was already headed toward a completely perimeter-less security environment before the COVID-19 pandemic hit. Now, the agency has gone full-fledged into a virtually wide-open landscape where physical constraints that used to exist have been largely eradicated, and new types of threats against its workforce, tools, supply chains, and operations abound.
Cloud-computing models provide an edge on the connected battlefield - Story
February 10, 2021By Mike Epley
The ability to collect and analyze data from radar; intelligence, surveillance, and reconnaissance (ISR); electronic warfare (EW); and other sensors at the edge can offer the U.S. military a decisive advantage on the battlefield. Yet resource and operational constraints continue to stand in the way. Applying cloud-native models can help overcome these constraints and improve decision-making while in theater.
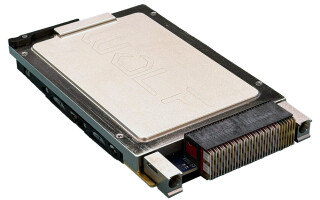
Securing military embedded systems is a giant challenge - Story
October 08, 2020Updating and patching security vulnerabilities to limit the attack surface for the military’s embedded systems – especially legacy ones – can be a daunting task.