Wind River

Wind River's VxWorks played critical role in Artemis II space mission - News
April 13, 2026WALNUT CREEK, Calif. The VxWorks platform from Wind River (an Aptiv company) was the software enabling reliable, real-time performance for the recently returned Artemis II mission, the company reported.
Time-Sensitive Networking e-Book: Leading editorial on the impact of Time-Sensitive Networking in military applications - Whitepaper
June 02, 2025Mission-critical military sensor systems including, avionics, ground vehicle systems, uncrewed vehicles, and communications systems need connectivity between modules or devices that is deterministic so decisions can be made in real-time to respond to complex threats.
Managing the data deluge: How military radar systems are getting smarter - Story
February 12, 2025Every second, military radar systems collect terabytes of data about potential threats in the skies above. But having data isn’t the same as having intelligence. In an age of information overflow, the U.S. Department of Defense faces a new kind of challenge: turning this tsunami of radar data into actionable battlefield insights.
SAIC/Wind River partnership expands accelerate mission-critical systems development - News
October 15, 2024WASHINGTON. Officials at Science Applications International Corp. (SAIC) and Wind River joined hands in an expanded strategic partnership to deliver industry-leading technologies to government customers by easing mission-oriented integration, speeding development, and enhancing functionality in systems, for the U.S. Army and other government entities, including cabinet-level departments and independent agencies. The announcement was made at the AUSA Annual Meeting in Washington this week at the Washington Convention Center.
Wind River Helix Virtualization Platform achieves conformance to FACE Technical Standard, Edition 3.2 Safety Base Profile - News
October 02, 2024ALAMEDA, Calif. Wind River, a global leader in delivering software for the intelligent edge, today announced that Wind River Helix Virtualization Platform has achieved conformance to the latest Future Airborne Capability Environment, or FACE, Technical Standard, Edition 3.2.
Comms
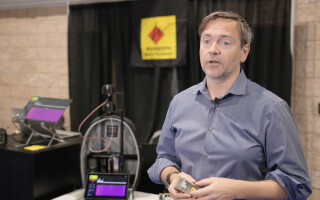
Wind River expert gives overview of Time Sensitive Networking whitepaper launch at MOSA Summit - Video
June 18, 2024Michel Chabroux, Vice President Product Management at Wind River talks to Tom Varcie with Military Embedded Systems about a whitepaper collaboration on Time Sensitive Networking at the MOSA Summit 2024 in National Harbor.
FACE-conformant digital cockpit display demoed at MOSA Summit by Curtiss-Wright, Wind River, others - News
June 17, 2024NATIONAL HARBOR, Maryland. Curtiss-Wright, in collaboration with Wind River, Ansys, and CoreAVI, is demonstrating a new digital cockpit flight display at this year's MOSA Industry & Government Summit & Expo.