The consolidation of federated systems into a modular open system approach (MOSA) changes the way helicopter avionics systems operate, interface, and communicate with one another. New capabilities can be quickly inserted, resilient technologies can be emphasized, and digital beamforming antennas expand applications.
Military Embedded Systems
Op-Eds
GUEST BLOG: The worldwide market for unmanned aerial vehicles - Blog
April 30, 2024WARFARE EVOLUTION BLOG. Previously, we studied the markets for fighter planes and bombers, ground combat vehicles and tanks, warships and submarines, and unmanned naval vessels (surface and underwater). Now, it’s time to explore the market for unmanned aerial vehicles (UAVs), which is rapidly becoming the largest volume segment of the military platforms. First, the UAV designation is actually a misnomer.
Common MOSA, SOSA 2.0 Snapshot 2 - Blog
March 27, 2024While it was officially released in the famous Dept. of Defense Tri-Service Memo five years ago, the concept of a modular open systems approach (MOSA) has been around for some time and is not a new concept, said Jason Dirner, in his keynote address at the MOSA [Modular Open Systems Approach] Virtual Summit held February 22 and hosted by myself and Military Embedded Systems. What is new, however, Dirner said, is “common MOSA, [where] you have multiple programs and services conforming to the same standard,” which enables a greater level of reuse and portability across the community.
GUEST BLOG -- The metaverse, AI, and space defense: Emerging tech transforming 2024 - Blog
March 12, 2024As we settle into 2024, emerging technologies continue to transform how we experience the digital world and beyond. The metaverse promises more immersive and interactive virtual environments through innovations in augmented reality (AR), virtual reality (VR) and generative artificial intelligence (AI). At the same time, AI and machine learning (ML) are proving invaluable in enhancing military operations and national security priorities like space defense.
GUEST BLOG: Industry 5.0 -- The digital transformation of A&D manufacturing confronts the next phase - Blog
March 12, 2024Aerospace and defense (A&D) manufacturers caught up with implementing Industry 4.0 technologies and processes, but now they are facing a new evolution coming in the form of Industry 5.0. The newest iteration could have a number of implications for A&D manufacturers – from cobots and build-to-order to assistive wearables and hyperglobization pullback. The upshot? The humans are back in charge.
The worldwide market for unmanned naval vessels - Blog
February 29, 2024WARFARE EVOLUTION BLOG. In our last escapade, we investigated the worldwide market for warships and submarines. Out of respect for the literary principle of subject matter continuity, we are forced to explore the worldwide market for UNVs (unmanned naval vessels) in this essay, since they are an extension of warships and submarines. UNVs break down into two basic groups: unmanned surface vessels (USV) and unmanned underwater vehicles (UUV). We will deal with naval unmanned aerial vehicles (NUAV) in another composition.
GIVING BACK: NextOp - Blog
February 13, 2024Each issue, the editorial staff of Military Embedded Systems will highlight a different organization that benefits the military, veterans, and their families. We are honored to cover the technology that protects those who protect us every day.
GUEST BLOG: Bringing data processing to the extraterrestrial edge - Blog
February 13, 2024When it comes to data processing and analysis, space is a final frontier that’s filled with challenges. Fortunately, military leaders have access to the technology and tools to make interstellar data processing a success, resulting in faster actionable insights – and a strategic and tactical advantage.
Talking electronic warfare trends, requirements, AOC with Jerome Patoux of ADI - Blog
December 11, 2023We’re here on the first day of the 60th Annual AOC International Symposium & Convention, held at the Gaylord Convention Center in National Harbor, Maryland. Electronic warfare (EW), spectrum dominance, and signals intelligence and the RF, microwave, and signal-processing technologies behind them are key components of both the conference and the exhibition.
For a take on the AOC event, and a look at the EW market, I sat down with Jerome Patoux, Director of Aerospace & Defense for the Aerospace, Defense, and RF Products Business Unit of Analog Devices. Here are some excerpts:
GUEST BLOG: Worldwide Market for Warships and Submarines - Blog
November 29, 2023WARFARE EVOLUTION BLOG. In previous episodes, we explored the two largest military platform markets: ground combat vehicles and tanks, and fighter planes and bombers. This time, we’ll take a look at the third market for big iron: warships and submarines. I’m going to throw a lot of numbers around in this composition but don’t take them as absolute. Warships sink all the time (Ukraine has sunk or damaged 17 Russian ships in the war so far), and shipyards are launching a new warship now and then. So, look at these numbers as estimates. Let’s start from the top.
GIVING BACK: Hope for The Warriors - Blog
November 21, 2023Each issue, the editorial staff of Military Embedded Systems will highlight a different organization that benefits the military, veterans, and their families. We are honored to cover the technology that protects those who protect us every day.
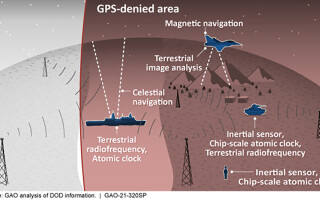
GUEST BLOG: Navigating modern warfare: PNT beyond GPS - Blog
November 21, 2023The issue of position, navigation, and timing (PNT) plays a pivotal role in the effectiveness and precision of modern weapons systems, making PNT indispensable in contemporary warfare.
GUEST BLOG: Enabling warfighter collaboration with cross-domain solutions - Blog
October 12, 2023Last year, the U.S. Department of Defense (DoD) declared integrated deterrence one of its key themes. In the simplest terms, integrated deterrence refers to the DoD’s ability to share information seamlessly between branches, allies, partners, and classification levels.
DSEI busy place for embedded electronics companies - Blog
September 15, 2023LONDON. It's been four years since I was last here, having missed the first event post-COVID in 2021, but I found this year’s DSEI the best one I’ve attended in terms of activity among embedded electronics suppliers, success in terms of our daily newsletter from the show, and the most smooth experience I’ve ever had in terms of getting to and from the show each day.
FACE and MOSA gaining traction across the Atlantic - Blog
September 14, 2023LONDON. Many questions on open architecture initiatives and the Department of Defense (DoD) modular open systems approach (MOSA) mandate were being floated to U.S. embedded hardware and software suppliers at DSEI in London this week. So, over dinner last night, I asked Chip Downing, Outreach Committee Co-chair of the Future Airborne Capability Environment (FACE) Consortium and Senior Market Development Director for Aerospace and Defense at RTI, what type of open architecture strategies are being pursued by European defense departments and if the U.S initiatives like FACE influenced those efforts.
-
KC-46 tanker upgrades to be accelerated by U.S. Air Force, Boeing
May 13, 2026
-
Night vision goggles to be supplied to U.S. Army by Elbit America
May 12, 2026
-
Advanced T-7A Red Hawk jet trainer cleared for production by U.S. Air Force
May 08, 2026
-
Closing the adoption gap in MOSA-driven avionics modernization
May 07, 2026
Unmanned
-
Special Operations and drone tech
May 19, 2026
-
SNC and Fairlead partner to produce AEGIR uncrewed surface vessels
May 19, 2026
-
AFSOC unveils 'Havoc Spear' cruise missile at SOF Week
May 19, 2026
-
BlackSea Technologies brings Comet unmanned surface vessel to SOF Week
May 19, 2026
-
How holographic 3D radar technology can improve C-UAS efforts
May 13, 2026
-
Dual-band RF transceiver released by Analog Devices
May 13, 2026
-
Best In Show awards at XPONENTIAL 2026 show: Excellence in RF & microwave, AI/ML
May 13, 2026
-
J-Squared Technologies expanding Ottawa site with 26K sq.ft. of new space for defense manufacturing and testing
May 11, 2026
-
SOF Week 2026 Preview | Aviation, Drones & the Future of Special Operations (video)
May 18, 2026
-
2026 USSOCOM Capability Demonstration live, May 20 in Tampa
May 18, 2026
-
USSOCOM Commander Bradley to keynote SOF Week 2026
May 15, 2026
-
Wireless networking technology for autonomous systems to be showcased by Doodle Labs at SOF Week
May 15, 2026